Attackers can force Echos to hack themselves with self
By A Mystery Man Writer
Description
Popular “smart” device follows commands issued by its own speaker. What could go wrong?

How to Secure Your Home Network

API security, vulnerabilities and common attacks

s Alexa reports 'Alexa versus Alexa', an attack method that
The Mirai Confessions: Three Young Hackers Who Built a Web-Killing

Attackers can force Echos to hack themselves with self

Defcon 2018: Echo hack turned speaker into spy bug - Gearbrain
Ryan Montgomery The Hacker Who Hunts Child Predators Part Two

Pew! Pew! Researcher Uses Laser to Steal Data From a Tiny Chip

Denial-of-service attack - Wikipedia
What is a Cyber Attack? Definition and Related FAQs

Active Defense: Security Operations Evolved > The Cyber Defense
How would you hack me? As someone trying to protect themselves

The inside story of the world's most dangerous malware - E&E News
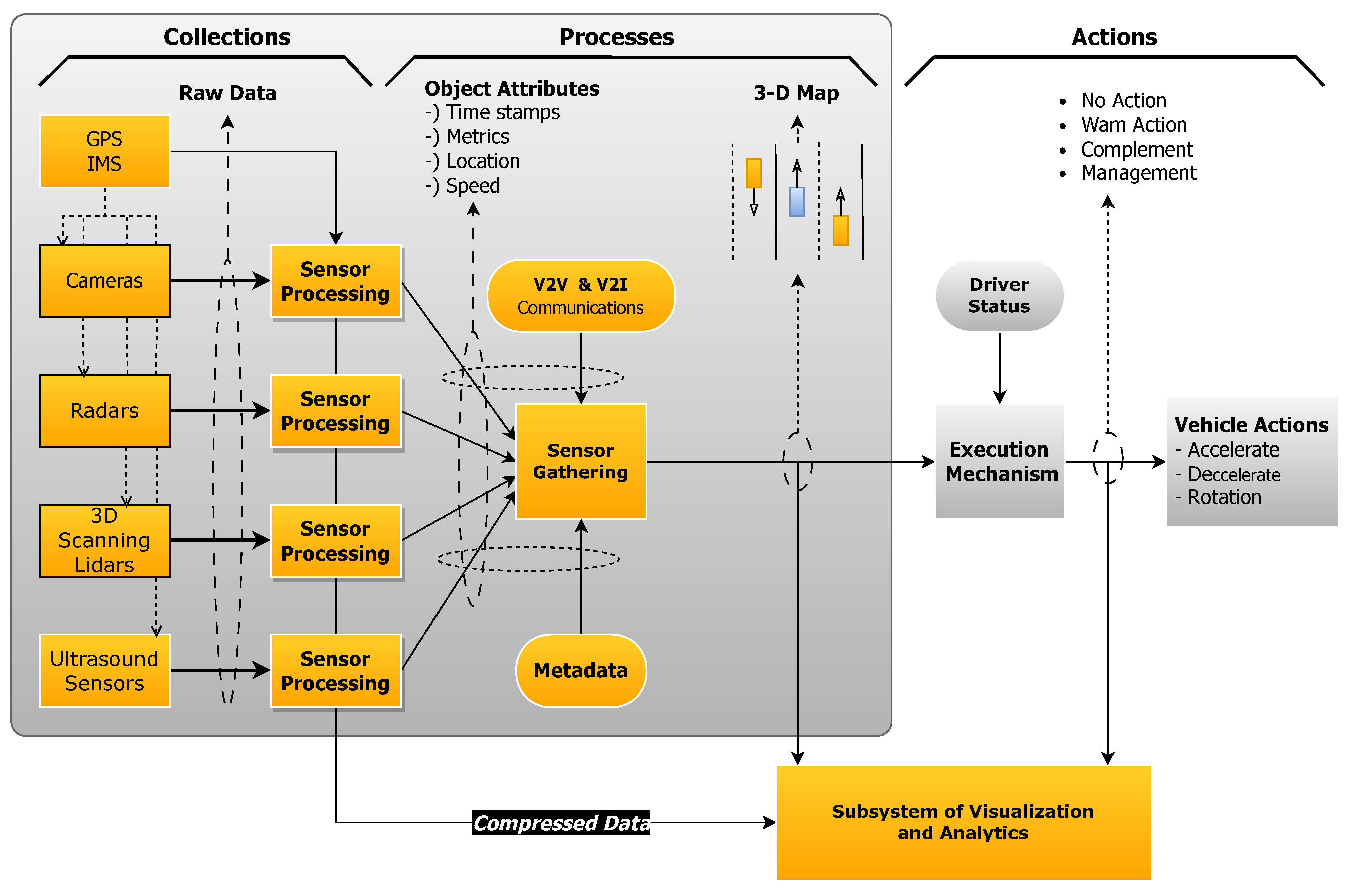
pub.mdpi-res.com/jcp/jcp-03-00025/article_deploy/h
from
per adult (price varies by group size)







