Layer 8 Security
By A Mystery Man Writer
Description
Layer 8 Security | 1,985 followers on LinkedIn. Solving data risk management challenges with practical security, compliance, and privacy strategies. | Layer 8 Security is a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for your evolving information security and compliance needs. Today’s business environment requires seamless integration with third-party vendors, clients, and partners. We ensure your information ecosystem is secure, compliant and resilient to the severity and frequency of a disruption resulting from a cyber attack.
Layer 8 Security is a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for your evolving information security and compliance needs. Today’s business environment requires seamless integration with third-party vendors, clients, and partners. We ensure your information ecosystem is secure, compliant and resilient to the severity and frequency of a disruption resulting from a cyber attack. The Layer 8 Security philosophy is focused on the human layer of cybersecurity. where business processes and technology intersect. As the cyber threats evolve in sophistication so must the defenses of companies, starting with its people. We are passionate about what we do. We refer to ourselves as Sheep Dogs; we feel a benevolent call to help others.
Layer 8 Security is a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for your evolving information security and compliance needs. Today’s business environment requires seamless integration with third-party vendors, clients, and partners. We ensure your information ecosystem is secure, compliant and resilient to the severity and frequency of a disruption resulting from a cyber attack. The Layer 8 Security philosophy is focused on the human layer of cybersecurity. where business processes and technology intersect. As the cyber threats evolve in sophistication so must the defenses of companies, starting with its people. We are passionate about what we do. We refer to ourselves as Sheep Dogs; we feel a benevolent call to help others.

Layer 8 Security - Securing the Nut Between the Keyboard & Screen

Layer 8 Security on LinkedIn: #layer8security #cybersecurity #datasecurity #cybersecurityawareness…

Base @ The Layer 8 - Base Cyber Security
The need for Layer 8: Why the OSI model isn't enough for

Philadelphia Business Journal Veterans of Influence Rising Star Awards 2022: Sean Toolan, Layer 8 Security - Philadelphia Business Journal

Layer 8
Layer 8

8th Layer Insights

Layer 8 Security - the Human Firewall
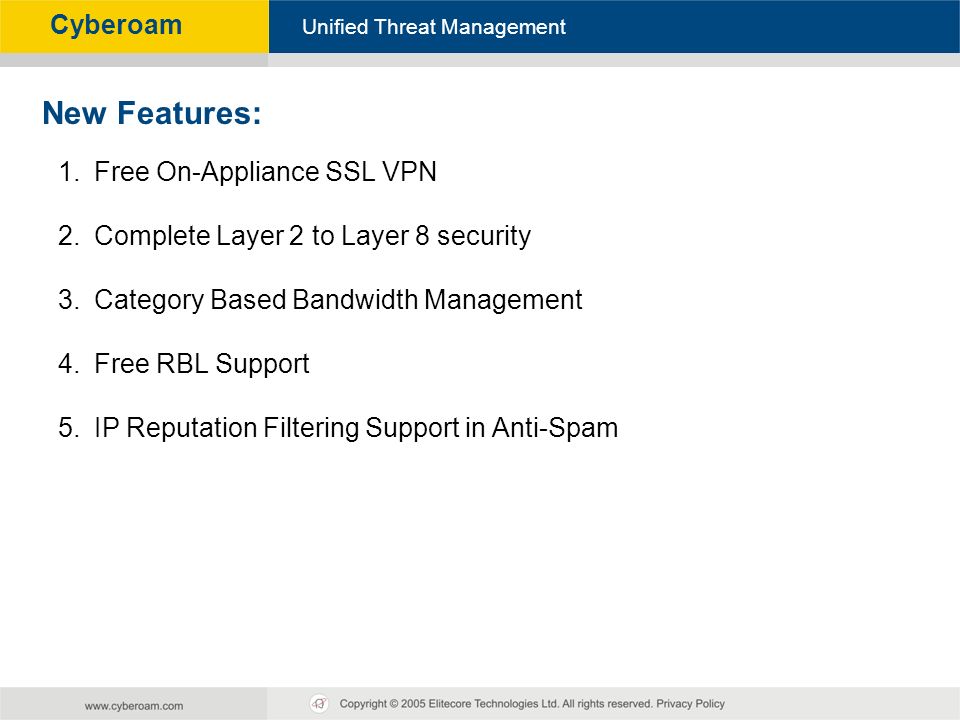
Cyberoam - Unified Threat Management Unified Threat Management Cyberoam Cyberoam Upgrade Training v9.6 build ppt download

Layer 8

Phishing Layer 8: The Human Layer - Libraesva Security Blog

Layer 8 Security stories - TechDay New Zealand

Future of IoT with 5G Technology
from
per adult (price varies by group size)







