Human vs. Non-Human Identity in SaaS
By A Mystery Man Writer
Description
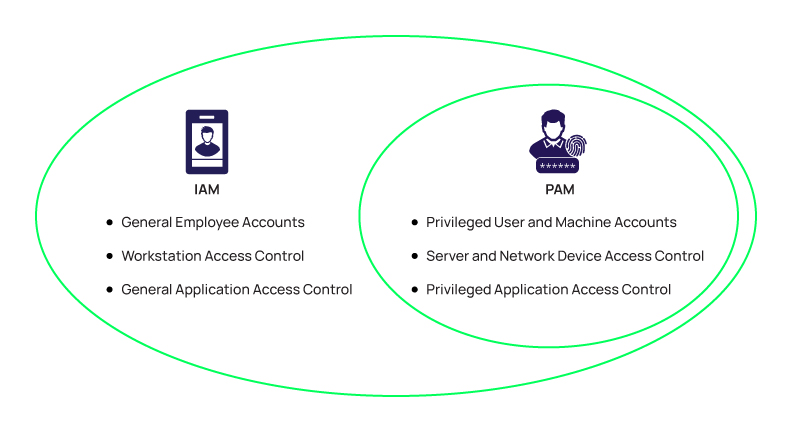
What is Identity and Access Management (IAM)?

Five Common Authentication and Authorization Mistakes to Avoid in

Dustin Crossman on LinkedIn: Human vs. Non-Human Identity in SaaS

Identity Defined Security Best Practices

The consequences of SaaS sprawl: A real-world study

Log4Pot - A honeypot for the Log4Shell vulnerability ⋆ DarkSideOps
Human vs. Non-Human Identity in SaaS

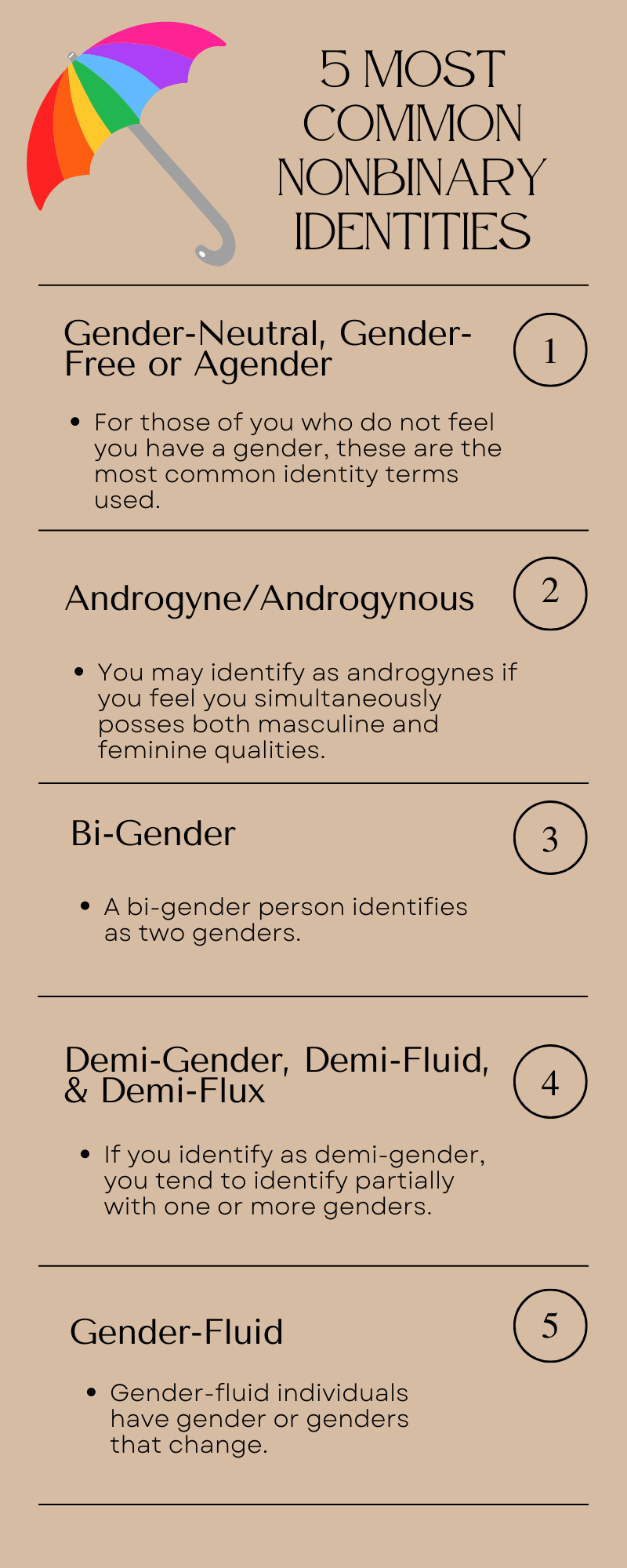
What are Non-Human Identities?

A History of Human Identity in Pictures – Part 1
from
per adult (price varies by group size)